- Published on
- •2 min read
Diffie-Hellman Explained: How Two People Share Secrets Over Public Channels
- Authors

- Name
- Pulathisi Kariyawasam
Introduction
The Diffie-Hellman key exchange is one of the most elegant solutions in cryptography. It solves a seemingly impossible problem: How can two people agree on a secret key over a public channel where everyone can listen?
This mathematical "magic" is at the heart of modern secure communications - from HTTPS websites to secure messaging apps. Let's explore how it works, step by step, from intuitive analogies to the mathematical reality.
Stage 1: The Problem
Question: How can two people share a secret number over an OPEN line where everyone can listen?
The Challenge:
- Alice and Bob need to agree on a secret SESSION KEY
- But an attacker (Eve) is listening to EVERY message they send
- If they send the key directly, Eve hears it and can decrypt everything
Let's use a simple analogy first, then show the real math.
Stage 2: Paint Analogy (Simple Version)
Imagine mixing paint colors:
Setup (known to everyone, including attacker):
Yellow paint = 5 (This is the "public color" - everyone knows it)
Alice's Secret
Alice picks: Red paint = 3
Alice mixes:
Red (3) + Yellow (5) = Orange
Orange is sent to Bob
Bob's Secret
Bob picks: Blue paint = 7
Bob mixes:
Blue (7) + Yellow (5) = Green
Green is sent to Alice
Now the magic happens:
Alice receives Green from Bob
- Alice adds her Red (3) to Green
- Result: Green + Red = BrownGreen
Bob receives Orange from Alice
- Bob adds his Blue (7) to Orange
- Result: Orange + Blue = BrownGreen
✓ SAME COLOR!
- ✓ Eve only sees Orange and Green
- ✓ Eve cannot reverse the mixing to find the original Red and Blue
Key insight: The final color depends on BOTH secrets (Red and Blue) AND the public color (Yellow). Mixing is one-way Eve can't unmix the colors to recover the secrets.
Stage 3: Real Math (Modular Arithmetic)
Paint colors are too simple. Real Diffie-Hellman uses modular exponentiation. Don't worry about understanding the math just see the pattern.
Setup (public, everyone knows):
p = 23 (a prime number)
g = 5 (the "generator")
These are like the "yellow paint" - public knowledge
Alice's Calculation
Alice's secret: a = 6
Alice calculates:
A = g^a mod p
A = 5^6 mod 23
A = 8
Alice sends 8 to Bob
Bob's Calculation
Bob's secret: b = 15
Bob calculates:
B = g^b mod p
B = 5^15 mod 23
B = 19
Bob sends 19 to Alice
Eve sees: 8 and 19. But she only knows g=5 and p=23. Can she recover a=6 or b=15? No! This is the "discrete logarithm problem" it's practically impossible for large numbers.
Stage 4: Computing the Shared Secret
Now Alice and Bob each compute the SAME session key using the numbers they received.
Alice's Calculation
Alice has:
- Her secret:
a = 6 - Bob's number:
B = 19
Alice calculates:
S = B^a mod p
S = 19^6 mod 23
S = 2
Bob's Calculation
Bob has:
- His secret:
b = 15 - Alice's number:
A = 8
Bob calculates:
S = A^b mod p
S = 8^15 mod 23
S = 2
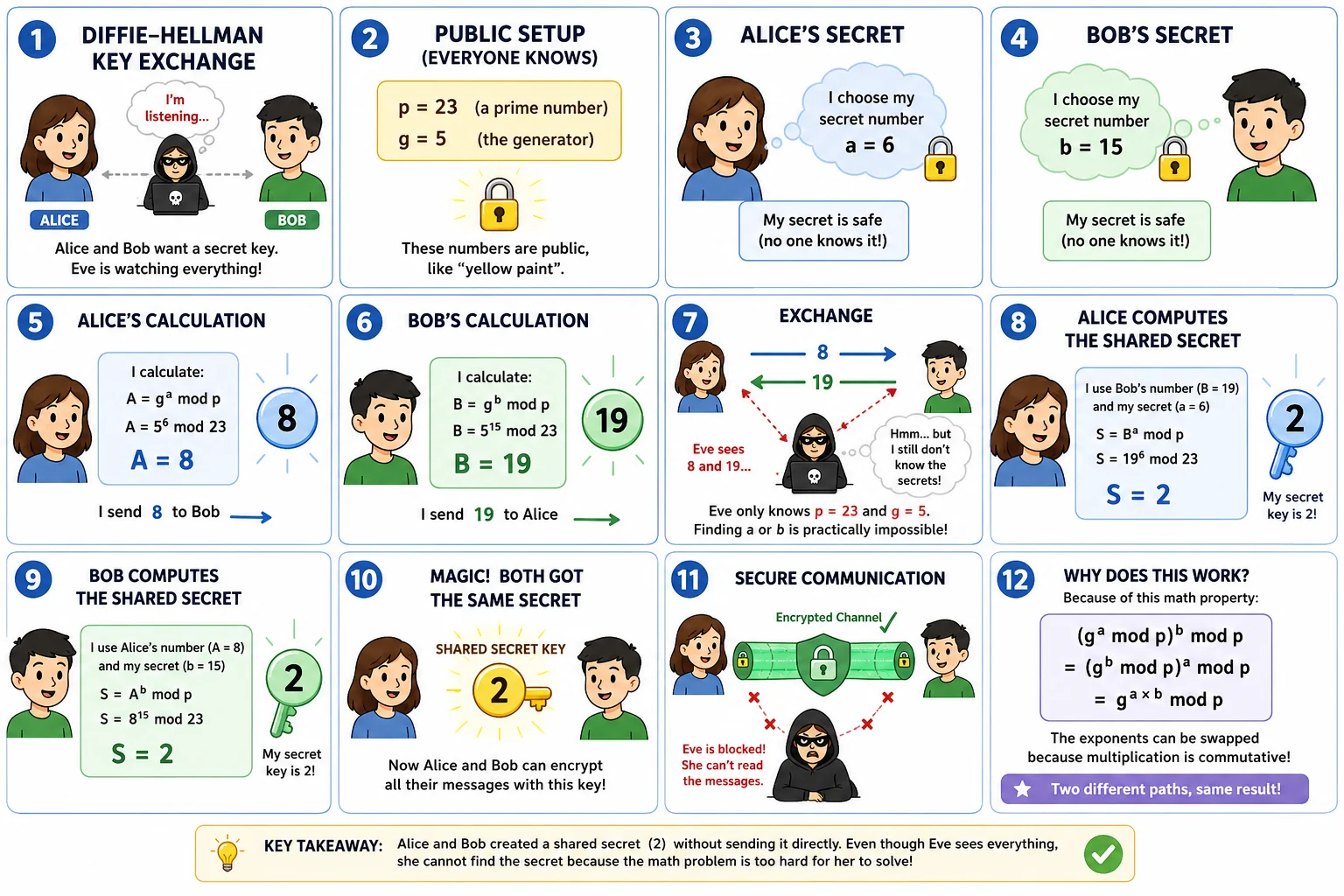
✓ Magic! Both got the same number: 2
This is the session key. Now they can encrypt all data with it.
Why does this work? Mathematically, both computations equal:
(g^a mod p)^b mod p = (g^b mod p)^a mod p = g^(a×b) mod p
The exponents can be swapped because multiplication is commutative!
Stage 5: Why the Attacker Can't Break It
Eve (the attacker) knows:
p = 23g = 5A = 8(Alice sent this)B = 19(Bob sent this)
Eve needs to find: a and b
The problem: She needs to solve:
5^a mod 23 = 8 → What is a?
For small numbers, Eve could try all possibilities (brute force). But in real TLS, these numbers are 2048 bits long!
Real TLS parameters:
g = 2(small)p = 2048-bit prime= huge number with 600+ digits
For Eve to find a, she'd need to try ~10^600 different values. Even if her computer checks 1 billion per second:
Time needed = 10^591 years
(The universe is only 13.8 billion years old!)
✓ Unbreakable:
The discrete logarithm problem (reversing g^a mod p) is computationally impossible with current technology. This is why Diffie-Hellman is secure.
What Eve sees in the data stream:
| Public Info | Eve Can See? | Can Eve Use It? |
|---|---|---|
| p, g | ✓ Yes | ✗ No use alone |
| A = g^a mod p | ✓ Yes | ✗ Can't reverse to find a |
| B = g^b mod p | ✓ Yes | ✗ Can't reverse to find b |
| Session Key = g^(a×b) mod p | ✗ No |
Perfect! Now you have an interactive step-by-step explanation of Diffie-Hellman
Let me explain the key points in simple terms:
The Core Idea (In Plain English)
Think of it like this: Imagine Alice and Bob both have magic paint that works in a very special way:
- Public Paint (everyone knows): Yellow
- Alice's Secret: She picks Red
- Bob's Secret: He picks Blue
The "Magic":
- When you mix colors with the secret number, the order DOESN'T MATTER
- Alice mixing Red + Yellow gives the same final color as Bob mixing Blue + Yellow (if done in a special mathematical way)
- But Eve can only see the mixed colors, not the original Red or Blue
Why It Works Mathematically
The real magic uses modular exponentiation:
- Alice knows:
a(her secret) andg^b mod p(Bob's public number) - Bob knows:
b(his secret) andg^a mod p(Alice's public number)
Alice calculates: (g^b)^a mod p
Bob calculates: (g^a)^b mod p
Mathematically, these are EQUAL because:
(g^b)^a = g^(b×a) = g^(a×b) = (g^a)^b
So they both get the same session key, even though:
- ✓ The session key was NEVER transmitted
- ✓ Each person only sent public numbers
- ✓ Eve has no way to reverse the math with current computers
Why the Attacker Fails
- Eve sees:
g,p,A = g^a mod p, andB = g^b mod p - Eve needs to find:
aorb - The Problem: This is called the Discrete Logarithm Problem. It means:
- We can easily compute
g^a mod p(exponentiation is fast) - But reversing it (logarithm) is practically impossible for large numbers
- Even the world's fastest computer would take millions of years
- We can easily compute
After Diffie-Hellman
Once Alice and Bob have the shared session key, they stop using public/private key cryptography entirely. They use symmetric encryption (AES) with the session key to encrypt all their messages. This is fast and doesn't require any more key exchange.
Mathematical Properties
Why Modular Arithmetic?
Modular arithmetic provides the "one-way" property that makes Diffie-Hellman secure:
Easy direction (exponentiation):
Given: g, a, p
Compute: g^a mod p
Time: Fast (polynomial time)
Hard direction (discrete logarithm):
Given: g, g^a mod p, p
Find: a
Time: Exponential (practically impossible for large numbers)
The Mathematics Behind the Magic
The key mathematical property is:
(g^a mod p)^b mod p = (g^b mod p)^a mod p = g^(ab) mod p
This works because of the properties of modular exponentiation:
- Associative:
(x^y)^z = x^(yz) - Commutative:
ab = ba
Security Requirements
For Diffie-Hellman to be secure:
- p must be prime - ensures the mathematical group has the right properties
- p must be large - makes discrete logarithm computationally infeasible
- g must be a generator - ensures the full keyspace can be reached
- Secrets a,b must be random - prevents predictable keys
Real-World Implementation
In TLS Handshakes
When you see this in TLS output:
Server Temp Key: X25519, 253 bits
This means:
- X25519: Modern elliptic curve version of Diffie-Hellman
- 253 bits: Size of the secret numbers
- Temporary: New secrets generated for each connection (forward secrecy)
Performance Comparison
| Operation | RSA 2048-bit | ECDH P-256 | X25519 |
|---|---|---|---|
| Key Generation | Slow | Medium | Fast |
| Key Exchange | Slow | Medium | Fast |
| Security Level | 112-bit | 128-bit | 128-bit |
| Key Size | 2048 bits | 256 bits | 256 bits |
X25519 is the modern standard because it's both fast and secure.
Conclusion
Diffie-Hellman key exchange is a masterpiece of mathematical elegance:
- Solves an impossible problem: Sharing secrets over public channels
- Based on hard mathematics: Discrete logarithm problem
- Computationally practical: Fast for legitimate users
- Computationally infeasible: Impossible for attackers
- Forward secure: New secrets for each session
Understanding Diffie-Hellman helps you appreciate why modern cryptography works and why we can trust secure connections even over untrusted networks.
The next time you see "TLS handshake" or "key exchange" in your logs, you'll know there's beautiful mathematics working behind the scenes to keep your data safe.
Further Reading
- Original Paper: "New Directions in Cryptography" by Diffie & Hellman (1976)
- RFC 7748: Elliptic Curves for Security (X25519/X448)
- Discrete Logarithm Problem: Mathematical foundations of cryptography
- Elliptic Curve Cryptography: Modern, efficient version of Diffie-Hellman
